CISM Training – Certified Information Systems Manager
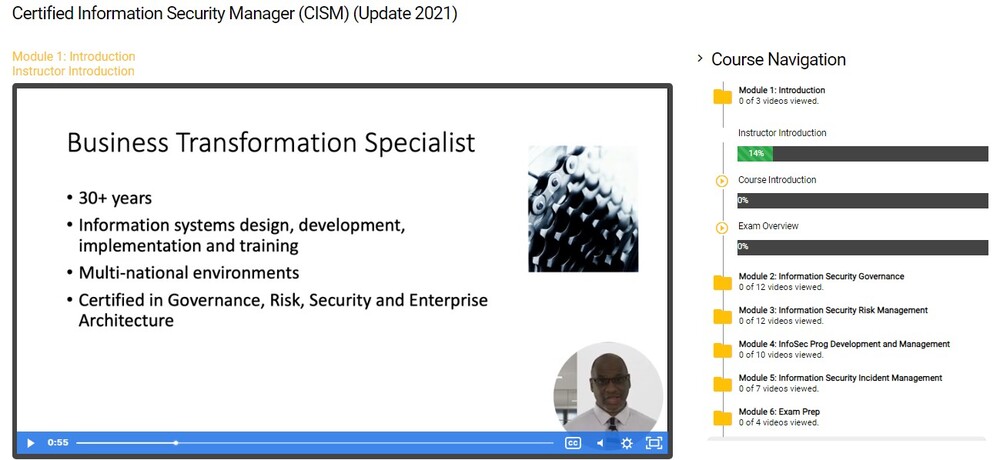
Are you ready to take your cybersecurity career to new heights? The CISM Training – Certified Information Systems Manager course is your gateway to becoming an exceptional security professional. Led by the esteemed instructor, Roger St Hilaire, who boasts an impressive 30+ years of industry expertise and an impressive array of certifications including CISM, CGEIT, MOF, TOGAF & PSP-Rainmaker Foundation Certifications, this course is a game-changer!
Step into the world of advanced-level cybersecurity training designed to sharpen your on-the-job skills and equip you with the knowledge needed to conquer the Certified Information Systems Manager (CISM) certification exam. Once you’ve completed your PenTest+, CySA+, and various higher-level certifications in Cisco and Microsoft, you’re ready for the ultimate challenge.
So, what sets CISM Training apart? Let’s dive into the benefits:
Unleash Your Potential: This course is your launchpad to reach the pinnacle of the security management field. Become a recognized leader who can confidently manage, design, and oversee an enterprise’s information security program. With CISM, doors of opportunity swing wide open!
Unparalleled Expertise: Learn from the best in the business. Roger St Hilaire, a seasoned veteran with over three decades of experience, will guide you through the intricate world of information systems management. His wealth of knowledge combined with his diverse certifications makes him an invaluable mentor.
Comprehensive Curriculum: Master the essential concepts, methodologies, and best practices crucial for success in today’s ever-evolving cybersecurity landscape. From risk management to incident response, governance to compliance, this course covers all the critical areas you need to excel.
Real-World Application: Gain practical, hands-on skills that can be immediately applied in your workplace. The CISM Training bridges the gap between theory and practice, empowering you to implement effective security strategies, protect valuable assets, and safeguard against emerging threats.
Prestigious Certification: Achieving the CISM certification is a testament to your expertise and dedication to the field. It not only validates your skills but also enhances your professional credibility, opening doors to exciting career advancements and higher earning potential.
But wait, there’s more! Let’s talk about the exam:
The CISM certification exam is a formidable challenge, but fear not – our course has got you covered. With Roger St Hilaire as your guide, you’ll receive comprehensive exam preparation. From in-depth content review to practice exams and valuable insights, you’ll be equipped with the confidence and knowledge to conquer the exam with ease.
Don’t let this opportunity pass you by. Join the ranks of elite security professionals and embark on a journey of personal and professional growth. Enroll in the CISM Training – Certified Information Systems Manager course today and become a force to be reckoned with in the world of cybersecurity!
The following list of major topics, which spans the four domains of CISM practice and the associated tasks, will be covered throughout the course. The Certified Information Systems Manager Exam Preparation Course Outline for Online Training:
- Information Security Defined
- Information Security Principles
- Support the Business
- Defend the Business
- Promote Responsible Security Program Development and Security Behavior
DOMAIN 1 – Knowledge of Security Governance, Information Security Governance and Security Policies
- Section One: Designing a Strategy and Governance Framework
- Section Two: Gaining Management Approval
- Section Three: Implementing the Security Strategy
DOMAIN 2 – Information Security Risk Management and Security Requirements
- Section One: Risk Identification
- Section Two: Risk Analysis and Treatment
- Section Three: Risk Monitoring and Reporting and Monitoring of Security Activities
DOMAIN 3 – Information Security Management and Security Program Development
- Section One: Alignment and Resource Management
- Section Two: Standards Awareness and Training
- Section Three: Building Security into Processes and Practices
- Section Four: Security Monitoring and Reporting
DOMAIN 4 – Information Security Incident Management
- Section One: Planning and Integration
- Section Two: Readiness and Assessment
- Section Three Identification and Response
- Exam Techniques
ISACA Requirements for Certification:
- To facilitate the student’s understanding of ISACA’s approach to information security, and its related concepts such as risk.
- Develop an understanding of key practices in the governance, management of risk, program development, and incident management in the realm of information security.
- Ensure that the student is appropriately prepared for successful completion of the Certified Information Security Manager exam given by ISACA on the first attempt.
Prerequisites Requirements CISM: Certified Information Security
To acquire the distinguished certification of a Certified Information Security Manager (CISM), you must submit evidence verifying at least five years of experienced information security managers in data security, 3-year information security management requirement more specifically dedicated to security experience spread across multiple security business model disciplines. This job practice analysis must be completed within 10 years leading up to your CISM application date, or within 5 short years from when you initially passed the exam.
Course Outline:
Certified Information Security Manager (CISM)
Module 1: Introduction
Instructor Introduction
Course Introduction
Exam Overview
Module 2: Information Security Governance
Module Overview
InfoSec Strategic Context Part 1
InfoSec Strategic Context Part 2
GRC Strategy and Assurance
Roles and Responsibilities
GMA Tasks Knowledge and Metrics
IS Strategy Overview
Strategy Implementation
Strategy Development Support
Architecture and Controls
Considerations and Action Plan
InfoSec Prog Objectives and Wrap-Up
Module 3: Information Security Risk Management
Module Overview
Risk Identification Task and Knowledge
Risk Management Strategy
Additional Considerations
Risk Analysis and Treatment Tasks & Knowledge
Leveraging Frameworks
Assessment Tools and Analysis
Risk Scenario Development
Additional Risk Factors
Asset Classification and Risk Management
Risk Monitoring and Communication
Information Risk Management Summary
Module 4: InfoSec Prog Development and Management
Module Overview
Alignment and Resource Management – Task and Knowledge
Key Relationships
Standards Awareness and Training – Tasks and Knowledge
Awareness and Training
Building Security into Process and Practices – Tasks and Knowledge
Additional Technology Infrastructure Concerns
Security Monitoring and Reporting Overview Tasks and Knowledge
Metrics and Monitoring
Summary
Module 5: Information Security Incident Management
Module Overview
Planning and Integration Overview Task and Knowledge
Incident Response Concepts and Process
Forensics and Recovery
Readiness and Assessment – Overview Tasks and Knowledge
Identification and Response Overview Tasks and Knowledge
Incident Processes
Module 6: Exam Prep
Case Study – Security On a Shoestring Budget
Case Study – APT In Action
Summary
Exam Prep
Frequently Asked Questions About CISM Training – Certified Information Systems Manager
What can I expect from the CISM Training Online Course?
What main areas does the CISM IT Training Course cover?
Who is the instructor for this IT Training Course?
What are the prerequisites for the CISM Training Online Course?
What modules does the CISM IT Training Course include?
What type of content does the online course offer?
Your Training Instructor

Roger St Hilaire
CISM, CGEIT, CRISC, TOGAF, Certified Trainer and Governance Specialist
Roger is an experienced IT professional with a proven track record of designing and managing large-scale technology systems. Successfully designed the first knowledge engine for the UNDP Sub-Regional Resource Facility, known as the Request Tracker, which facilitated workflow-based tracking of queries and increased productivity. Managed and grew a $70 million USD dual data center national network system for the Trinidad and Tobago government, expanding it from 400+ sites to 512 and increasing customer satisfaction. Skilled in vendor negotiations, securing approximately $200K USD in committed support during a crisis event. Adept in saving clients money and improving their operations, saving one BPR client $60K USD and improving their security processes. Committed to driving positive change and delivering results in fast-paced and dynamic environments.




Reviews
There are no reviews yet.