Embark on an exhilarating journey into the realm of cybersecurity with the Certified Ethical Hacker (CEH) course! EC-Council proudly presents CEH 12, the latest iteration of our cutting-edge training program that will unleash your potential as a skilled ethical hacker. Get ready to acquire the coveted CEH certification and become a formidable force in the world of network and information security!
This course is your passport to an exciting and dynamic career, where you’ll immerse yourself in the world of ethical hacking. Through hands-on exploration, you’ll uncover vulnerabilities, scan targets, and analyze cyber threats with precision. Our expert instructors will guide you step-by-step, sharing their invaluable insights and equipping you with the latest tools and techniques used by ethical hackers.
What sets CEH 12 apart is its emphasis on real-world application. Every lesson is infused with captivating, real-life scenarios that challenge you to break into target organizations and networks. As you navigate through intricate puzzles and overcome obstacles, you’ll collect tangible evidence of your success, all while staying invisible to the unaware. It’s like being the star of your very own cyber espionage thriller!
We understand the importance of hands-on experience in mastering ethical hacking skills. That’s why we provide you with a comprehensive setup guide, allowing you to create a fully immersive virtual environment. With real hardware and software-based tools at your fingertips, you’ll sharpen your expertise in a risk-free space, readying yourself for any cybersecurity battleground.
To ensure your mastery of the subject matter, CEH 12 integrates practice exam test questions throughout the course. This reinforcement strategy hones your knowledge retention, giving you the confidence to face the final certification exam with unwavering certainty. With the CEH certification in your hands, you’ll possess a validation of your skills and knowledge that employers in the industry highly respect.
During your CEH journey, you’ll unlock a treasure trove of hacking prowess. Unleash the power of Metasploit Framework and Kali Linux, your trusted companions in testing a wide array of attacks. Explore Exploit-DB, GitHub, and other cutting-edge platforms to stay ahead of the game and leverage the latest exploit codes. With your newfound arsenal, you’ll become a force to be reckoned with, adept at uncovering vulnerabilities and keeping malicious hackers at bay.
As you progress through the course, you’ll gain the ability to implement effective security controls, ensuring the protection of your network against malevolent forces. By mastering the techniques of ethical hacking, you’ll join the ranks of skilled professionals who actively combat cyber threats and safeguard critical infrastructure.
Don’t miss this opportunity to redefine your career and become a Certified Ethical Hacker! Join us in the CEH 12 course, where you’ll unravel the mysteries of cybersecurity, outsmart adversaries, and forge a path of success in the ever-evolving world of ethical hacking. Enroll today and unlock the door to endless possibilities!
Why you should take Ethical Hacking Training?
Discover the thrilling world of ethical hacking and propel your cybersecurity career to new heights with our cutting-edge online training for CEH v12 certification. This immersive course puts you in the driver’s seat of penetration testing, equipping you with the skills and knowledge needed to combat modern cyber threats.
Not only does this comprehensive training cover all the essential objectives of the CEH 312-50 exam, but it also goes above and beyond, providing you with extensive hands-on practice and real-world scenarios. Prepare to unleash your full potential as you delve into the exciting realm of ethical hacking courses, mastering the art of identifying vulnerabilities and securing computer systems and networks.
By obtaining your CEH credential, you gain a rock-solid foundation in cybersecurity threats, bolstering your professional profile and unlocking a world of exciting career opportunities. Employers around the globe recognize the CEH certification as a mark of excellence in the industry, paving the way for exciting roles in penetration testing, vulnerability assessment, and ethical hacking.
But this course is more than just a certification prep. It’s a thrilling journey into the world of cybersecurity, where you’ll explore the latest hacking concepts and cutting-edge techniques. Our expert instructors will guide you through every step, ensuring you acquire the practical skills and confidence necessary to excel in real-world scenarios.
And that’s not all! Alongside the training, you’ll gain access to our extensive blog, “Cybersecurity Career Path: Skills, Roles & Opportunities.” This valuable resource will provide you with invaluable insights into the cybersecurity industry, helping you navigate the vast array of career options and set yourself on a path to success.
Are you ready to seize the opportunity to become a cybersecurity trailblazer? Join our online training for CEH v12 today and become a master of ethical hacking. Prepare to unlock a world of possibilities and embark on an exhilarating journey where you will defend against cyber threats, safeguard organizations, and shape the future of cybersecurity. Your exciting new career awaits!
Combine CEH with PenTest+ and Become A Penetration Tester
Introducing cutting-edge Penetration Testing course, your gateway to mastering the art of cybersecurity and information security. Prepare to take your skills to exhilarating new heights as you embark on an immersive journey, transforming into an elite penetration tester who can uncover hidden vulnerabilities in systems, networks, and data.
In this comprehensive course, you’ll delve deep into the world of penetration testing, learning advanced techniques and strategies that enable you to safeguard digital landscapes with unmatched precision. Our expert instructors, armed with extensive industry experience, will guide you through real-world scenarios, equipping you with the practical knowledge needed to excel in this thrilling field.
With the Penetration Testing course, you’ll gain an in-depth understanding of diverse attack vectors, exploring the very same methods used by malicious hackers to exploit system weaknesses. But fear not! Your newfound knowledge will be put to ethical use, as you harness it to fortify networks and fortify organizations against potential cyber threats.
As a student, you’ll benefit from hands-on labs and engaging exercises that simulate realistic environments, allowing you to put your skills to the test. Armed with a suite of cutting-edge tools and methodologies, you’ll learn to assess network security, identify vulnerabilities, and execute targeted penetration tests. This practical experience will empower you to confidently navigate the complex landscape of cybersecurity, making you an invaluable asset to any organization.
To validate your newfound expertise, the Penetration Testing course offers an optional certification exam. Successfully passing the exam will demonstrate your proficiency in the field, providing tangible evidence of your skills and enhancing your career prospects. Armed with this reputable certification, you’ll be well-equipped to seize lucrative opportunities in today’s ever-expanding IT industry.
Furthermore, the earning potential in this field is truly remarkable. Penetration testers are in high demand, with their expertise being a critical asset for organizations seeking to protect their valuable assets. With the skills acquired in this course, you’ll open doors to a six-figure salary, enjoying a rewarding career that combines intellectual stimulation with financial stability.
Don’t miss your chance to unlock a world of endless possibilities in the exciting realm of cybersecurity. Join the Penetration Testing course today and embark on a thrilling journey that will propel your career to extraordinary heights. Together, let’s fortify digital landscapes and safeguard our interconnected world.
Who Benefits from taking our Online Training Ethical Hacking Courses?
This course is intended for IT security professionals, Cybersecurity professionals and those with cyber range and specialized skills focused on security professionals in the following IT careers:
- Ethical hacker
- Cybersecurity Analyst
- Cybersecurity Consultant
- White Hat Hacker
- System Administrator
- Network Administrator
- Engineer
- Web manager
- Security Analyst
- Security Consultant
- Auditors
- Security Professionals
- and anyone else working in the cybersecurity industry.
Prerequisites For Our CEH Training Course:
Introducing the CEH Cybersecurity Certification: Unleash Your Inner Ethical Hacker!
Are you ready to embark on an exciting journey into the world of cybersecurity? Look no further than the Certified Ethical Hacker (CEH) course, the ultimate training experience for aspiring cybersecurity professionals. This course is designed to equip you with the skills and knowledge to ethically hack, uncover vulnerabilities, and fortify the digital fortresses of organizations.
Get ready to explore a thrilling blend of networking wizardry and cutting-edge web and network security principles. Whether you’re a seasoned IT professional or a tech enthusiast, the CEH course is your passport to becoming a sought-after cybersecurity expert.
What makes the CEH course stand out from the rest? It doesn’t require any specific prerequisites, making it accessible to anyone with a burning curiosity to learn. However, having prior exposure to vendor-neutral concepts taught in CompTIA Network+ and CompTIA Security+ courses can give you an extra edge.
Throughout the CEH journey, you’ll delve into a comprehensive curriculum that dives deep into the art of ethical hacking. From understanding the mind of a malicious attacker to mastering the latest defense mechanisms, you’ll gain invaluable insights and hands-on experience.
But that’s not all! The CEH course empowers you to push the boundaries of cybersecurity by providing a virtual playground for experimentation. To fully unleash your potential, you’ll need a 64-bit PC with VMware Workstation Player virtualization, a minimum of 8 GB of RAM (though 16 GB is preferred), and 100 GB of free disk space. With this powerful setup, you’ll be ready to explore the realms of ethical hacking in a secure and controlled environment.
And here’s the icing on the cake: after completing the course, you’ll have the opportunity to prove your mettle through the CEH certification exam. This globally recognized certification validates your skills and serves as a testament to your expertise in ethical hacking. Stand out from the crowd and open doors to exciting career opportunities in the ever-evolving field of cybersecurity.
Join us on this thrilling adventure and become a guardian of digital systems. Unleash your inner ethical hacker with the CEH Cybersecurity Certification. Your journey starts here!
FAQs About Certified Ethical Hacker Training for the Certification Exam
Is Certified Ethical Hacker worth it?
Yes, Certified Ethical Hackers (CEH) are an excellent investment that can help you gain valuable skills. CEH provides both technical knowledge and an important qualification for your future career.
How do I become CEH certified?
Becoming a Certified Ethical Hacker (CEH) involves several steps. While the process can vary, the general steps to become a CEH are as follows:
- Training: Enroll in a Certified Ethical Hacker (CEH) course. This training typically involves five days of intensive instruction. The course covers various aspects of cybersecurity and information security threats, as well as practical hacking techniques. It aims to provide you with the knowledge and skills needed to work as a certified ethical hacker.
- Self-Study: In addition to the training course, it’s essential to engage in self-study to deepen your understanding of the subject matter. This includes reading books, articles, and online resources related to ethical hacking, cybersecurity, and information security. Stay updated with the latest industry trends and emerging threats.
- Exam: Once you have completed the training and feel prepared, you can register for the CEH exam. The exam consists of 125 multiple-choice questions, and you will have a limited amount of time to complete it. The exam evaluates your understanding of ethical hacking concepts, tools, techniques, methodologies, and best practices.
- Continuing Professional Education (CPE) Credits: After passing the CEH exam, you need to maintain your certification by earning Continuing Professional Education (CPE) credits. Within three years of obtaining the CEH certification, you must accumulate 120 CPE credits. These credits demonstrate your commitment to continuous learning and staying up-to-date with the evolving field of ethical hacking.
- CPE Activities: To earn CPE credits, you can engage in various activities such as attending industry conferences, writing research papers, teaching training classes in a related domain, reading materials on related subject matters, attending webinars, and participating in relevant professional organizations. Each activity typically has a specific credit value associated with it, and you need to document your participation and completion of these activities to claim the credits.
It’s worth noting that the specific requirements and processes for becoming a CEH may vary slightly based on the certification provider and any updates to the certification program. It’s always recommended to refer to the official guidelines and requirements provided by the certification provider for the most accurate and up-to-date information.
How long does it take to become a Certified Ethical Hacker?
That information about the Certified Ethical Hacker (CEH) certification exam and training is correct. The CEH certification is offered by the EC-Council (International Council of E-Commerce Consultants) and is designed to validate individuals’ skills and knowledge in the field of ethical hacking and cybersecurity.
To become a Certified Ethical Hacker, you have two options for meeting the prerequisites:
- Option 1: Attend Official Training: You can attend an official 5-day training course provided by the EC-Council or any of their authorized training partners. This training covers various aspects of ethical hacking and prepares you for the certification exam. After completing the training, you become eligible to take the exam.
- Option 2: Self-Study and Experience: If you prefer to study on your own or already have relevant knowledge and experience, you can submit an eligibility application to EC-Council. You need to provide proof of at least two years of work experience in the information security domain and pay a non-refundable application fee. Once your application is approved, you can directly take the CEH certification exam.
Regarding the exam itself, it is a 4-hour computer-based exam consisting of 125 multiple-choice questions. The exam tests your understanding of different areas of ethical hacking, such as footprinting and reconnaissance, scanning networks, system hacking, social engineering, web application penetration testing, and more. To pass the exam and obtain the CEH certification, you must achieve a minimum passing score set by EC Council.
The time it takes to prepare for the CEH certification training and exam can vary greatly depending on your prior knowledge, experience, and study habits. If you have a strong background in cybersecurity, it might take you less time to prepare compared to someone who is relatively new to the field. Typically, individuals spend anywhere from a week to several months preparing for the training and exam.
Lastly, it’s important to note that certification requirements and details may change over time. It’s recommended to visit the official EC-Council website or contact them directly for the most up-to-date information on the CEH certification process.
How much does the CEH certification cost?
The Certified Ethical Hacker (CEH) certification is indeed a popular certification for individuals interested in pursuing a career in ethical hacking and cybersecurity. While I don’t have the exact and up-to-date pricing information for the course, you can typically expect to pay varying costs depending on the training provider and the specific package or options you choose.
Contact them directly to get the most accurate and current pricing details for their Certified Ethical Hacker Certification Training course.
Regarding the average salary for CEH holders, the figures you mentioned are within a reasonable range. However, it’s important to note that salaries can vary depending on several factors such as location, level of experience, industry, and specific job roles within the cybersecurity field. The salary estimates you mentioned, with most CEH holders earning between $45,000 and $129,000 per year, can serve as a general guideline, but individual circumstances may vary. It’s always a good idea to research current salary trends in your specific area and consult reputable sources for the most accurate information.
How long is the CEH certification valid, and how can I maintain it?
That is correct. The Certified Ethical Hacker (CEH) certification is valid for a period of three years from the date of certification. To maintain your certification, you are required to earn Continuing Professional Education (CPE) credits. These credits can be obtained through various activities that contribute to your professional development in the field of ethical hacking and information security.
Here are some common ways to earn CPE credits:
- Training Programs: Attending relevant training programs, workshops, or conferences organized by authorized training centers or industry events can earn you CPE credits.
- Webinars and Online Courses: Participating in webinars and completing online courses offered by recognized providers in the field can help you earn CPE credits.
- Writing Articles or Research Papers: Authoring articles, research papers, or whitepapers on topics related to ethical hacking or information security can contribute to your professional growth and earn you CPE credits.
- Professional Development Activities: Engaging in professional activities such as mentoring, teaching, presenting at conferences, or participating in industry forums can also earn you CPE credits.
- Active Participation: Actively participating in professional organizations, security groups, or forums related to ethical hacking and information security can be counted towards your CPE credits.
Course Outline:
Module 1: Introduction To Ethical Hacking
1.0 Introduction to CEH v12
1.1 Elements of Security
1.2 Cyber Kill Chain
1.3 MITRE ATT&CK Framework
1.3.1 Activity – Researching the MITRE ATTACK Framework
1.4 Hacking
1.5 Ethical Hacking
1.6 Information Assurance
1.7 Risk Management
1.8 Incident Management
1.9 Information Security Laws and Standards
1.10 Introduction to Ethical Hacking Review
Module 2: Footprinting and Reconnaissance
2.1 Footprinting Concepts
2.2 OSINT Tools
2.2.1 Activity – Conduct OSINT with OSR Framework
2.2.2 Activity – OSINT with the harvester
2.2.3 Activity – Add API Keys to the harvester
2.2.4 Activity – Extract Document Metadata with FOCA
2.2.5 Activity – Extract Document Metadata with FOCA
2.3 Advanced Google Search
2.3.1 Activity – Google Hacking
2.4 Whois Footprinting
2.4.1 Activity – Conducting Whois Research
2.5 DNS Footprinting
2.5.1 Activity – Query DNS with NSLOOKUP
2.6 Website Footprinting
2.6.1 Activity – Fingerprint a Webserver with ID Serve
2.6.2 Activity – Extract Data from Websites
2.6.3 Activity – Mirror a Website with HTTrack
2.7 Email Footprinting
2.7.1 Activity – Trace a Suspicious Email
2.8 Network Footprinting
2.9 Social Network Footprinting
2.10 Footprinting and Reconnaissance Countermeasures
2.11 Footprinting and Reconnaissance Review
Module 3: Scanning Networks
3.1 Scanning Concepts
3.2 Discovery Scans
3.2.1 Activity – ICMP ECHO and ARP Pings
3.2.2 Activity – Host Discovery with Angry IP Scanner
3.3 Port Scans
3.3.1 Activity – Port Scan with Angry IP Scanner
3.4 Other Scan Types
3.5 Scanning Tools
3.5.1 Activity – Hping3 Packet Crafting
3.5.2 Activity – Fingerprinting with Zenmap
3.6 NMAP
3.6.1 Activity – Nmap Basic Scans
3.6.2 Activity – Host Discovery with Nmap
3.6.3 – Activity – Nmap Version Detection
3.6.4 Activity – Nmap Idle (Zombie) Scan
3.6.5 Activity – Nmap FTP Bounce Scan
3.6.6 – Activity – NMAP Scripts
3.7 Firewall and IDS Evasion
3.7.1 Activity – Nmap Advanced Scans
3.8 Proxies
3.9 Scanning Countermeasures
3.10 Scanning Networks Review
Module 4: Enumeration
4.1 Enumeration Overview
4.2 SMB_NetBIOS_Enumeration
4.2.1 Activity – Enumerate NetBIOS Information with Hyena
4.3 File Transfer Enumeration
4.4 WMI Enumeration
4.4.1 – Activity – Enumerating WMI with Hyena
4.5 SNMP Enumeration
4.5.1 Activity – Enumerate WMI, SNMP, and Other Information Using SoftPerfect
4.6 LDAP Enumeration
4.7 DNS Enumeration
4.8 SMTP Enumeration
4.8.1 Activity – Enumerate Email Users with SMTP
4.9 Remote Connection Enumeration
4.10 Website Enumeration
4.10.1 Activity – Enumerate a Website with DirBuster
4.11 Other Enumeration Types
4.12 Enumeration Countermeasures and Review
Module 5: Vulnerability Analysis
5.1 Vulnerability Scanning
5.1.1 Vulnerability Scanning with OpenVAS
5.2 Vulnerability Assessment
5.3 Vulnerability Analysis Review
Module 6: System Hacking
6.1 System Hacking Concepts
6.2 Common OS Exploits
6.3 Buffer Overflows
6.3.1 Activity – Performing a Buffer Overflow
6.4 System Hacking Tools and Frameworks
6.4.1 Activity – Hack a Linux Target from Start to Finish
6.5 Metasploit
6.5.1 Activity – Get Started with Metasploit
6.6 Meterpreter
6.7 Keylogging and Spyware
6.7.1 Activity – Keylogging with Meterpreter
6.8 Netcat
6.8.1 Activity – Using Netcat
6.9 Hacking Windows
6.9.1 Activity – Hacking Windows with Eternal Blue
6.10 Hacking Linux
6.11 Password Attacks
6.11.1 Activity – Pass the Hash
6.11.2 Activity – Password Spraying
6.12 Password Cracking Tools
6.13 Windows Password Cracking
6.13.1 Activity – Cracking Windows Passwords
6.13.2 Activity – Cracking Password Hashes with Hashcat
6.14 Linux Password Cracking
6.15 Other Methods for Obtaining Passwords
6.16 Network Service Attacks
6.16.1 Activity – Brute Forcing a Network Service with Medusa
6.17 Post Exploitation
6.18 Pivoting
6.18.1 Activity – Pivoting Setup
6.19 Maintaining Access
6.19.1 Activity – Persistence
6.20 Hiding Data
6.20.1 Activity – Hiding Data Using Least Significant Bit Steganography
6.21 Covering Tracks
6.21.1 Activity – Clearing Tracks in Windows
6.21.2 Activity – View and Clear Audit Policies with Auditpol
6.22 System Hacking Countermeasures
6.23 System Hacking Review
Module 7: Malware Threats
7.1 Malware Overview
7.2 Viruses
7.3 Trojans
7.3.1 Activity – Deploying a RAT
7.4 Rootkits
7.5 Other Malware
7.6 Advanced Persistent Threat
7.7 Malware Makers
7.7.1 Activity – Creating a Malware Dropper and Handler
7.8 Malware Detection
7.9 Malware Analysis
7.9.1 Activity – Performing a Static Code Review
7.9.2 Activity – Analyzing the SolarWinds Orion Hack
7.10 Malware Countermeasures
7.11 Malware Threats Review
Module 8: Sniffing
8.1 Network Sniffing
8.2 Sniffing Tools
8.2.1 Activity- Sniffing HTTP with Wireshark
8.2.2 Activity – Capturing Files from SMB
8.3 ARP and MAC Attacks
8.3.1 Activity – Performing a MITM Attack with Ettercap
8.4 Name Resolution Attacks
8.4.1 Activity – Spoofing Responses with Responder
8.5 Other Layer 2 Attacks
8.6 Sniffing Countermeasures
8.7 Sniffing Review
Module 9: Social Engineering
9.1 Social Engineering Concepts
9.2 Social Engineering Techniques
9.2.1 Activity – Deploying a Baited USB Stick
9.2.2 Activity – Using an O.MG Lightning Cable
9.3 Social Engineering Tools
9.3.1 Activity – Phishing for Credentials
9.4 Social Media, Identity Theft, Insider Threats
9.5 Social Engineering Countermeasures
9.6 Social Engineering Review
Module 10: Denial-of-Service
10.1 DoS-DDoS Concepts
10.2 Volumetric Attacks
10.3 Fragmentation Attacks
10.4 State Exhaustion Attacks
10.5 Application Layer Attacks
10.5.1 Activity – Performing a LOIC Attack
10.5.2 Activity – Performing a HOIC Attack
10.5.3 Activity – Conducting a Slowloris Attack
10.6 Other Attacks
10.7 DoS Tools
10.8 DoS Countermeasures
10.9 DoS Review
Module 11: Session Hijacking
11.1 Session Hijacking
11.2 Compromising a Session Token
11.3 XSS
11.4 CSRF
11.5 Other Web Hijacking Attacks
11.6 Network-Level Session Hijacking
11.6.1 Activity – Hijack a Telnet Session
11.7 Session Hijacking Tools
11.8 Session Hijacking Countermeasures
11.9 Session Hijacking Review
Module 12: Evading IDS, Firewalls, and Honeypots
12.1 Types of IDS
12.2 Snort
12.3 System Logs
12.4 IDS Considerations
12.5 IDS Evasion
12.5.1 Activity – Fly Below IDS Radar
12.6 Firewalls
12.7 Packet Filtering Rules
12.8 Firewall Deployments
12.9 Split DNS
12.10 Firewall Product Types
12.11 Firewall Evasion
12.11.1 Activity – Use Social Engineering to Bypass a Windows Firewall
12.11.2 Activity – Busting the DOM for WAF Evasion
12.12 Honeypots
12.13 Honeypot Detection and Evasion
12.13.1 Activity – Test and Analyze a Honey Pot
12.14 Evading IDS, Firewalls, and Honeypots Review
Module 13: Hacking Web Servers
13.1 Web Server Operations
13.2 Hacking Web Servers
13.3 Common Web Server Attacks
13.3.1 Activity – Defacing a Website
13.4 Web Server Attack Tools
13.5 Hacking Web Servers Countermeasures
13.6 Hacking Web Servers Review
Module 14: Hacking Web Applications
14.1 Web Application Concepts
14.2 Attacking Web Apps
14.3 A01 Broken Access Control
14.4 A02 Cryptographic Failures
14.5 A03 Injection
14.5.1 Activity – Command Injection
14.6 A04 Insecure Design
14.7 A05 Security Misconfiguration
14.8 A06 Vulnerable and Outdated Components
14.9 A07 Identification and Authentication Failures
14.10 A08 Software and Data Integrity Failures
14.11 A09 Security Logging and Monitoring Failures
14.12 A10 Server-Side Request Forgery
14.13 XSS Attacks
14.13.1 Activity – XSS Walkthrough
14.13.2 Activity – Inject a Malicious iFrame with XXS
14.14 CSRF
14.15 Parameter Tampering
14.15.1 Activity – Parameter Tampering with Burp
14.16 Clickjacking
14.17 SQL Injection
14.18 Insecure Deserialization Attacks
14.19 IDOR
14.19.1 Activity – Hacking with IDOR
14.20 Directory Traversal
14.21 Session Management Attacks
14.22 Response Splitting
14.23 Overflow Attacks
14.24 XXE Attacks
14.25 Web App DoS
14.26 Soap Attacks
14.27 AJAX Attacks
14.28 Web API Hacking
14.29 Webhooks and Web Shells
14.30 Web App Hacking Tools
14.31 Hacking Web Applications Countermeasures
14.32 Hacking Web Applications Review
Module 15: SQL Injection
15.1 SQL Injection Overview
15.2 Basic SQL Injection
15.3 Finding Vulnerable Websites
15.4 Error-based SQL Injection
15.5 Union SQL Injection
15.5.1 Activity – Testing SQLi on a Live Website – Part 1
15.5.2 Activity – Testing SQLi on a Live Website – Part 2
15.6 Blind SQL Injection
15.7 SQL Injection Tools
15.7.1 Activity – SQL Injection Using SQLmap
15.8 Evading Detection
15.9 Analyzing SQL Injection
15.10 SQL Injection Countermeasures
15.11 SQL Injection Review
Module 16: Hacking Wireless Networks
16.1 Wireless Concepts
16.2 Wireless Security Standards
16.3 WI-FI Discovery Tools
16.4 Common Wi-Fi Attacks
16.5 Wi-Fi Password Cracking
16.6 WEP Cracking
16.6.1 Activity – Cracking WEP
16.7 WPA,WPA2,WPA3 Cracking
16.7.1 Activity – WPA KRACK Attack
16.8 WPS Cracking
16.9 Bluetooth Hacking
16.10 Other Wireless Hacking
16.10.1 Activity – Cloning an RFID badge
16.10.2 Activity – Hacking with a Flipper Zero
16.11 Wireless Security Tools
16.12 Wireless Hacking Countermeasures
16.13 Hacking Wireless Networks Review
Module 17: Hacking Mobile Platforms
17.1 Mobile Device Overview
17.2 Mobile Device Attacks
17.3 Android Vulnerabilities
17.4 Rooting Android
17.5 Android Exploits
17.5.1 Activity – Hacking Android
17.5.2 Activity – Using a Mobile Device in a DDoS Campaign
17.6 Android-based Hacking Tools
17.7 Reverse Engineering an Android App
17.8 Securing Android
17.9 iOS Overview
17.10 Jailbreaking iOS
17.11 iOS Exploits
17.12 iOS-based Hacking Tools
17.13 Reverse Engineering an iOS App
17.14 Securing iOS
17.15 Mobile Device Management
17.16 Hacking Mobile Platforms Countermeasures
17.17 Hacking Mobile Platforms Review
Module 18: IoT AND OT Hacking
18.1 IoT Overview
18.2 IoT Infrastructure
18.3 IoT Vulnerabilities and Threats
18.3.1 Activity – Searching for Vulnerable IoT Devices
18.4 IoT Hacking Methodology and Tools
18.5 IoT Hacking Countermeasures
18.6 OT Concepts
18.7 IT-OT Convergence
18.8 OT Components
18.9 OT Vulnerabilities
18.10 OT Attack Methodology and Tools
18.11 OT Hacking Countermeasures
18.12 IoT and OT Hacking Review
Module 19: Cloud Computing
19.1 Cloud Computing Concepts
19.2 Cloud Types
19.3 Cloud Benefits and Considerations
19.4 Cloud Risks and Vulnerabilities
19.5 Cloud Threats and Countermeasures
19.5.1 Activity – Hacking S3 Buckets
19.6 Cloud Security Tools And Best Practices
19.7 Cloud Computing Review
Module 20: Cryptography
20.1 Cryptography Concepts
20.2 Symmetric Encryption
20.2.1 Activity – Symmetric Encryption
20.3 Asymmetric Encryption
20.3.1 Activity – Asymmetric Encryption
20.4 Public Key Exchange
20.5 PKI
20.5.1 Activity – Generating and Using an Asymmetric Key Pair
20.6 Digital Signatures
20.7 Hashing
20.7.1 Activity – Calculating Hashes
20.8 Common Cryptography Use Cases
20.9 Cryptography Tools
20.10 Cryptography Attacks
20.11 Cryptography Review
20.12 Course Conclusion
Your Training Instructor

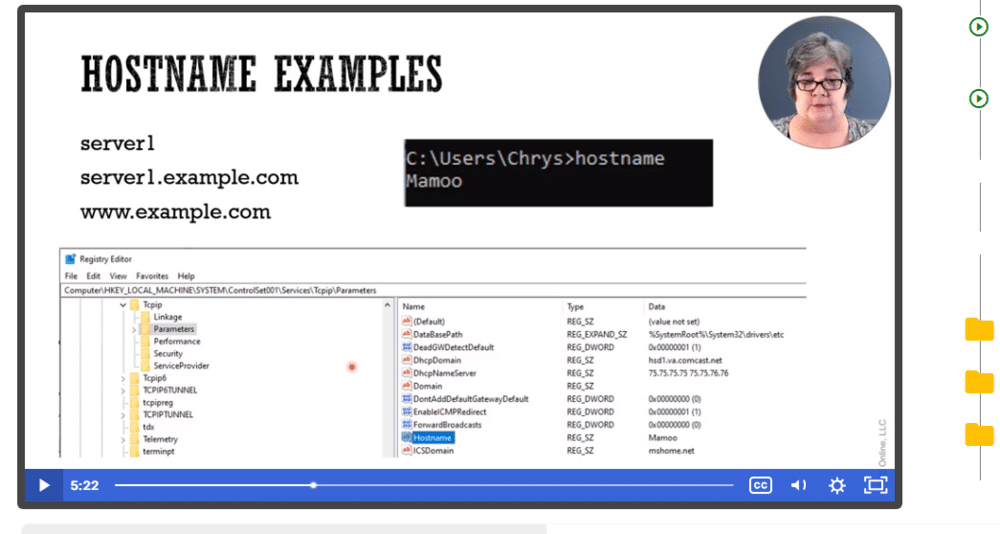
Chrys Thorsen
Education and Technology Expert
Chrys is an education and technology expert who specializes in enterprise-level IT infrastructure consulting and certified training of trainers. In her career, she has garnered 35 IT Certifications including Cisco CCSI/CCNP, CISSP, CISA, MCSE/MCITP, and many more. She has also authored 40 published certification textbooks and is currently working on the new CompTIA PenTest+ courseware.




Reviews
There are no reviews yet.